Corelan® Heap Exploitation Masterclass (Advanced)
Instructed by Peter Van Eeckhoutte
The Corelan “HEAP” exploit development MASTERCLASS (Advanced) is a fast-paced, mind-bending, hands-on course where you will learn advanced exploit development techniques from an experienced exploit developer. During this course, students will get the opportunity to learn how to write
exploits that bypass modern memory protections for the Win32 platform, using Windows 7 and Windows 10 as the example platform, but using techniques that can be applied to other operating systems and applications. We will discuss differences between Windows 7 and Windows 10 and explore previously undocumented techniques to achieve important exploitation primitives in Windows 10. The trainer will share his “notes from the field” and various tips & tricks to become more effective at writing exploits.
Classes are limited. Get registered!
This is most certainly not an entry level course. In fact, this is a one of the finest and most advanced courses you will find on Win32 exploit development. This hardcore, practical, hands-on course will provide students with solid understanding of x86 Windows heap exploitation. We make sure the course material is kept updated with current evolutions, includes previously undocumented tricks and techniques, and details about research we performed ourselves, so you can apply the research techniques on other applications and operating system versions. Combined with the way the course is built up, this will turn this class into a truly unique learning experience. During all of our courses, we don’t just focus on techniques and mechanics, we don’t focus on just using one vulnerability, but we mainly want to make sure you understand why a given technique is used, why something works and why something doesn’t work. In the advanced course, we provide you with generic insights on how to do your own research related with heap exploitation in general (not just Windows 7 or Windows 10), fully preparing you for the future. We believe those are just a few arguments that makes this training stand out between other exploit development training offerings. Feel free to check the testimonials page if you want to see real, voluntary, unmodified and uncensored reactions by some of our students. Finally, we offer you post-training support as well. If you have taken the course and you still have questions afterwards, we will help.
The current edition of the course is based on Windows 7 and Windows 10, and contains research and techniques that also work on Windows 11. (As the Windows 10/11 Heap Manager contains additional mitigations, we use Windows 7 first to teach the basics, and then use Windows 10/11 later on). Furthermore, this course contains an intro to x64 exploitation (stack & heap), providing you with the required fundamentals to get started with x64 exploitation yourself.
Learn the following key skills:
ASLR & DEP REFRESHER
WinDBG / WinDBGX (WinDBG Preview Edition)
Windows Heap Management
Heap Spraying
Heap Exploitation
Intro to x64 exploitation
What’s next
During the course, students will get the opportunity to work on real vulnerabilities in real applications, use a wide range of heap exploitation techniques and most importantly learn how to do your own research to find exploitation primitives in complex applications and new versions of Windows.

Advanced
In-person
June 17-20, 2024
September 9-12, 2024
4 days, 40 hours
Pentesters, auditors, network/system administrators, reverse engineers, malware analysts, developers, members of a security department, security enthusiasts, or anyone that has a solid and practical basic knowledge of exploit development for Windows already.
Requirements
All required tools and applications will be provided during the training or will be downloaded from the internet during the training.
You must have full administrator access to all machines. You must be able to install and remove software, and you must be able to disable and/or remove firewall/antivirus/… when necessary.
Prerequisites
Students must:
Why choose the Center for Cyber Security Training
Interactive, classroom-based learning
Subject matter experts
Trusted by US government agencies
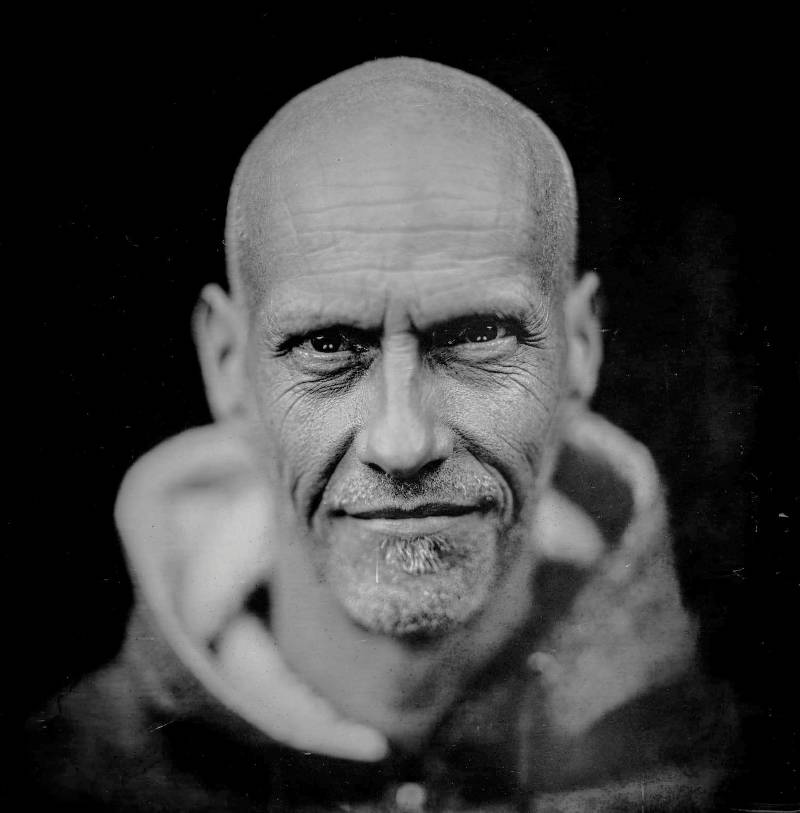
Peter Van Eeckhoutte
Probably the best exploit training on the planet. Why? The best teacher! He walks his talk and knows the topic like the back of his hands (or perchance, his tattooed arms). I encourage anyone who is passionate about exploit development to take this course. You will not regret it! A knowledgeable teacher/mentor/coach makes a BIG difference in tackling a difficult topic.- Jolly, Canada
Want more information?
Download the Exploit Development: Advanced course outline now.
Upcoming Training Sessions
June 5-8, 2023 (Columbia, MD) September 11-14. 2023 (Columbia, MD)
Classes are limited.
Enroll Now.
Related Courses
Our classroom delivers the most in-demand content from the highest profile subject matter experts. Intense and interactive, our courses prepare students with actionable insight and proven strategies.
Applied Data Science for Cyber Security
This interactive course teaches security professionals how to use data science techniques to quickly manipulate and analyze network and security data and ultimately uncover valuable insights. Topics range from data preparation to machine learning and implementation.

