Corelan® Stack Based Exploit Development
Instructed by Peter Van Eeckhoutte
The four-day “expert-level STACK based exploitation class (Bootcamp) introduces both basic and advanced techniques from Peter of Corelan. This course is a truly unique opportunity to learn both basic & advanced techniques from an experienced exploit developer. During this course students will be able to learn all ins and outs about writing reliable stack based exploits for the Windows platform. The trainer will share his “notes from the field” and various tips & tricks to become more effective at writing exploits.
We believe it is important to start the course by explaining the basics of stack buffer overflows and exploit writing, but this is most certainly not “your average” entry level course. In fact, this is a true bootcamp and one of the finest and most advanced courses you will find on Win32 stack based exploit development. This hardcore hands-on course will provide students with solid understanding of current stack based exploitation techniques and memory protection bypass techniques. We make sure the course material is kept updated with current techniques, includes previously undocumented tricks and techniques, and details about research we performed ourselves. Combined with the way the course is built up, this will turn this class into a truly unique experience. Learn directly from the author of mona.py The new current edition of the course is 100% based on Windows 10 and contains an introduction to x64 stack-based exploitation. During all of our courses, we don’t just focus on techniques and mechanics, but we also want to make sure you understand why a given technique is used, why something works and why something doesn’t work.
Learn the following key skills:
The x86 Environment
The Exploit Development Lab Environment
Stack Buffer Overflows
Egg Hunters
Reliability++ & Reusability++
Metasploit Framework Exploit Modules
ASLR
DEP
Intro to x64 exploitation

Beginner to Intermediate
In person
May 6-9, 2024 August 26-29, 2024
4 days, 32-40 hours
Pentesters, auditors, network/system administrators, reverse engineers, malware analysts, developers, members of a security department, security enthusiasts, or anyone interested in exploit development.
Requirements
All required tools and applications will be provided during the training or will be downloaded from the internet during the training.
You must have full administrator access to all machines. You must be able to install and remove software, and you must be able to disable and/or remove firewall/antivirus/… when necessary.
Prerequisites
Students should be:
Why choose the Center for Cyber Security Training
Interactive, classroom-based learning
Subject matter experts
Trusted by US government agencies
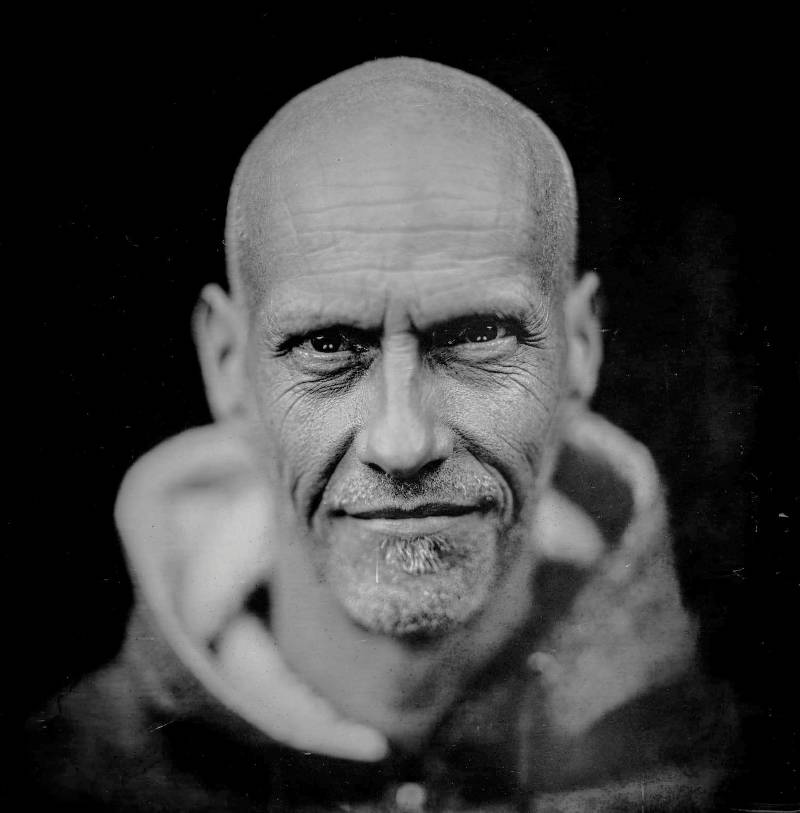
Peter Van Eeckhoutte
Peter Van Eeckhoutte is the founder of Corelan Team and the author of the well-known tutorials on Win32 Exploit Development Training. The team gathers a group of IT Security enthusiasts and researchers from around the world, who all share common interests : doing research, gather & share knowledge, and perform responsible/coordination disclosure. Above all, the team is well known for their ethics and their dedication to helping other people in the community. Together with the team, he has developed and published numerous tools that will assist pentesters and exploit developers, and published whitepapers/video’s on a wide range of IT Security related topics (pentesting tools, (malware) reverse engineering, etc).
You can find some of the tools on the Corelan github page.
Peter has been an active member of the IT Security community since 2000 and has been working on exploit development since 2006. He presented at various international security conferences (Athcon, Hack In Paris, DerbyCon, ISSA Belgium) and taught various Win32 Exploit Development courses at numerous places around the globe. He trained security enthusiasts & professionals from private companies, government agencies and military organizations.
Classes are limited. Get registered!
One of the most gruelling yet beneficial training courses that I have ever attended in my entire ofsec career! This course is definitely a good start for those who really want to get well acquainted with the basics of exploit development. On top of that, Peter is such an amazing instructor in terms of delivering his content and sharing with us some tips and tricks when facing problems during the lab exercises. Highly recommend.Hamzah, Singapore
Want more information?
Download the Exploit Development: Bootcamp course outline now.
Upcoming Training Sessions
May 1-4, 2023 (Columbia, MD) August 28-31, 2023 (Columbia, MD)
Classes are limited.
Enroll Now.
Related Courses
Our classroom delivers the most in-demand content from the highest profile subject matter experts. Intense and interactive, our courses prepare students with actionable insight and proven strategies.

Corelan® Exploit Development: Advanced
Our four-day advanced course will teach students how the Windows 7 and Windows 10 Heap Manager works, and how to write exploits for complex heap-related memory corruptions for the Win32 platform in a fast-paced, interactive learning environment. Master the techniques you need to succeed in the field.

Tactical Exploitation: Windows/Unix
In this intense five-day course, students will learn a variety of covert techniques used to enter secure commercial facilities. From lock picking and key decoding to RFID cloning and alarm sensor bypassing, students who demonstrate hands-on proficiency in key tactics will earn a Certificate of Completion.
