How did you get involved in cybersecurity training? Can you provide your background and education in the field?
I graduated as a software developer, but never really pursued a job based on that education.
Instead, during the last year at school, a friend of mine and I decided to open a small computer shop. He was primarily responsible for sales; I focused mainly on the technical and hardware side of things: the assembly of computers, setting up small network environments, providing support to small local companies, and so on. Around 2000, one of our clients reached out, asking for help because their PCs started to act up. I quickly discovered that someone infected the PCs with malware called “Back Orifice”. That event triggered my curiosity in information security.
I left that job shortly after, landed a job in a big international company and got promoted to “Security Officer” a few years later. Being able to focus on security topics also sparked my curiosity again, and I started doing research on buffer overflows and memory corruptions in my spare time. I took notes, posted my notes online, and that’s how the Corelan website was born.
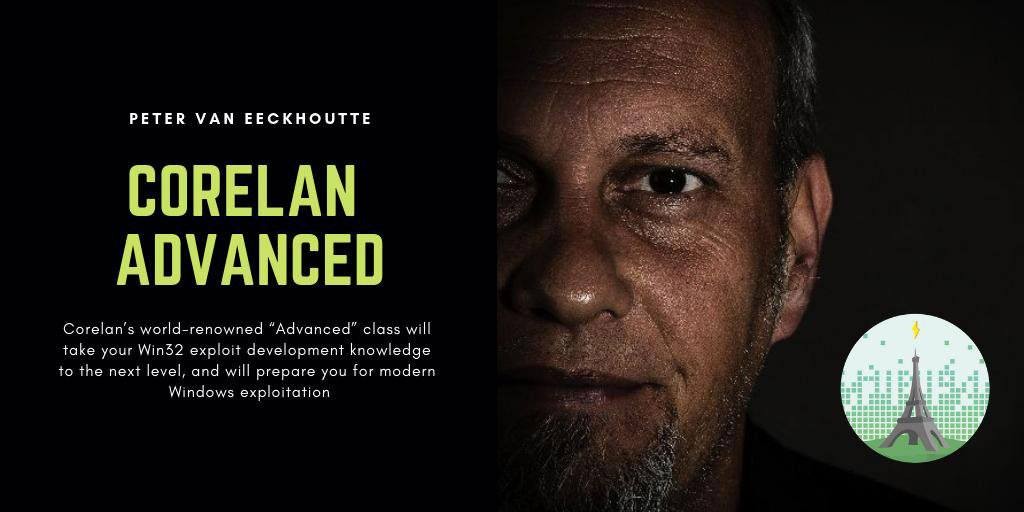
People reached out, expressed their appreciation for making my research available for free and suggested to consider turning the content into classes. And that’s exactly what I did. In 2010, I spent 6 months to create the first version of the Corelan “Bootcamp”, and I created the “Advanced” class a few years later. In October 2018, I left my corporate job, allowing me to focus entirely on Cybersecurity training and consulting.
What types of classes do you teach? What is your specialty?
I currently teach 2 classes, both of them focus on the exploitation of memory corruptions on the Microsoft Windows operating system. The bootcamp is a “beginner” class, and covers the exploitation of vulnerabilities that use the “stack”. The advanced class is based on the exploitation of “heap” vulnerabilities.
The Windows operating system has always been my main source of inspiration & research. Windows has evolved so much (and continues to evolve) and is much more secure than it has ever been. The efforts (and cost) to perform research, to find flaws, and to abuse those flaws have been increasing, and it really requires dedication and time to continue to understand protection mechanisms and to look for ways to bypass them. As a result, the number of people that possess the knowledge to build a working exploit for modern systems is decreasing. That may sound like a good thing, but it’s not. In fact, security mechanisms are based on an accurate understanding of how cybercriminals break into our systems. Hiding something doesn’t make things more secure. The goal of my classes is to teach essential skills, to demystify some of the Windows internals, to debunk common misconceptions and misunderstandings, and to teach and inspire people how to perform their own research.
By focusing entirely on the Windows operating system, I can make sure my classes are kept up-to-date, relevant, and of high quality. Those are, in my humble opinion, essential components of making sure that we can keep up with cybercriminals.
What would you consider the biggest threats to cybersecurity?
That’s a tough question, I don’t think there is a specific threat that stands out as being more important than the other ones. Context (threat vs what is important to you) is key.
To me, anything that touches people’s lives, their privacy, their wellbeing & security must clearly be taken seriously. Of course, it’s also (and obviously) important that society continues to operate, that delivery of critical services is guaranteed (electricity, water, etc), and that food & product safety is ensured as well, just to name a few things.
Overall, while companies give a lot of attention to providing easy/user-friendly access to computing devices and systems, the technology behind it has become incredibly complex. We don’t know where our data is, where these systems are, who has access to our data and whether or not the systems are really secure. And frankly, people don’t seem to care either, as long as “things work”. For some reason, the more complex a system, the more “trust” people seem to have in that system. We all continue to connect devices to the internet, exposing them to anyone else in the world, acting under the wrong assumption that “new” systems must be “secure” systems. Everybody expects some kind of absolute and mature level of “security”, as long as it doesn’t require them to change habits or to do anything at all. People seem to believe in the illusion of having a right to enjoy “flawless security by design”, something provided by someone else, so we can blame the other party if things go wrong.
Unfortunately, that’s not how things work. Designing & building complex technology is incredibly difficult, and security is not always part of the initial design either (for various reasons: short-term financial/economic reasons, ignorance, lack of awareness & training, etc).
On top of that, people make mistakes, and systems will continue to be vulnerable. At the same time, security professionals often struggle to implement (basic) security measures and are condemned to fighting an impossible & unfair battle. Systems continue to get hacked, (which sometimes goes unnoticed for many months), and cybercriminals (who often have more time & resources than those that are expected to protect our systems) can cause significant damage to the economy, to society and to you.
Overall, I believe we all put too much trust in others, in old and new technology. We often neglect to take responsibility for applying common sense, for adopting good practices that will help protect our own data & system, for being critical and accepting that we can’t always blame technology. Security is a common goal, a joint effort, but also a personal responsibility.
What training/course is in demand? What training SHOULD be in demand?
Any type of technology that is used on a large scale and/or used to protect critical/sensitive systems & information, will be targeted by criminals who want to steal information and/or to disrupt operations, for whatever reasons.
I would say that anything that focuses on the security of common operating system platforms (desktop, mobile, client-side and server-side) as well as emerging popular (web) technologies, should always be in demand.